Hello Readers, I hope you’re well.
Another week and another batch of cool features in Teams. The feature I’m focusing on today is App Setup Policies.
What are App Setup Policies?
App setup policies give admins a way to control how apps are displayed to users in Microsoft Teams. You can change the settings in the Global (Org-wide default) policy or you can create new policies for specific users or departments.
Admins can decide which apps are displayed on the left rail in Teams and which order they appear in.
Before app setup policies, you could still open another app by click on the ellipses under the lowest app in the list.
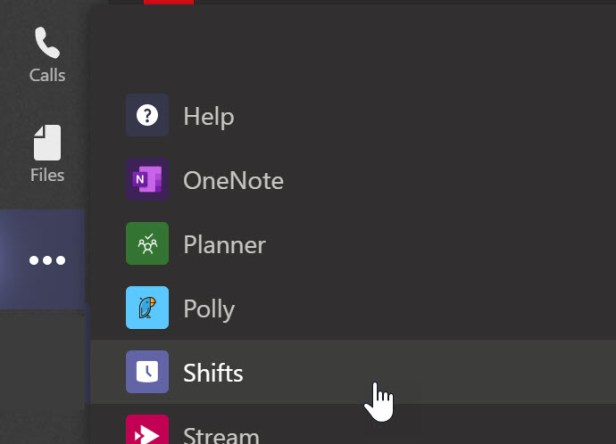
And you still can do this. But if there are apps that you’re in all the time. Wouldn’t it be great to add it to the rail for easy access? Now you can.
How to do it
Open up the Teams Admin Centre and expand Teams Apps and click on Setup Policies.
Modify the global policy
To modify the global policy, click on it

You’ll see a set of default apps

To add a pinned app, click on add apps

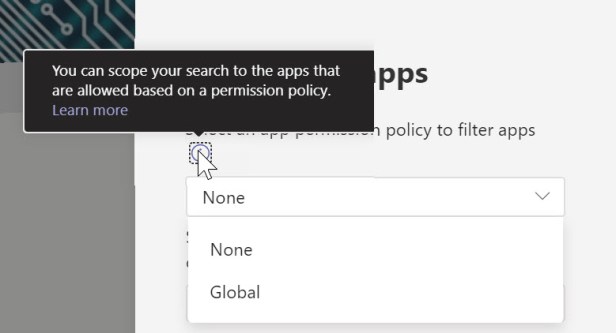
You can scope the search based on a permissions policy (I’ll explain that shortly). For now just choose global
If you want to look through the list of apps, just type a letter. “A” will be pretty common in the names of apps. Then you can scroll to find an app.

If you know the name of the app you want to pin, enter it in the search box. I’ve chosen Flow. Then click add
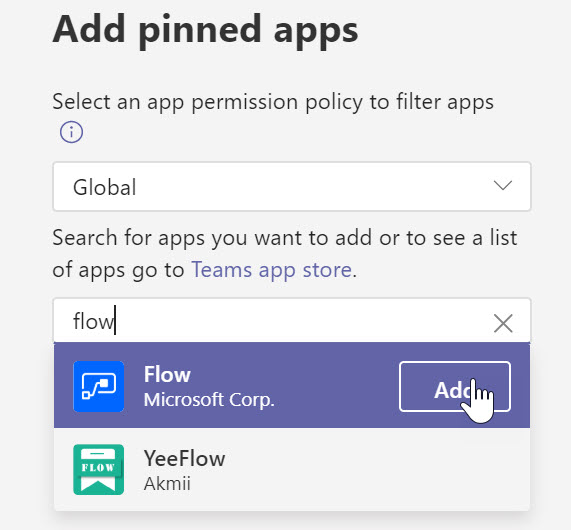
Repeat the search if you want to add more apps. Or just click add

You’ll see your app in the list. Click save to save the policy

Success

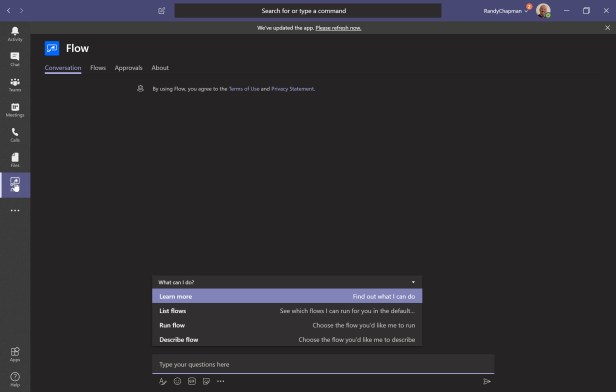
I had to wait a “Teams Minute” before the app showed up on my rail in Teams. I can’t exactly say how long because I first added the app yesterday. I did check periodically through the day, but in the browser, and it never turned up. Then I looked this morning and it was there. So that’s what I mean by Teams Minute. It could take an hour or a day or anything in between. Leave a comment if you can narrow down how long it takes.

When you click on the app in the rail, it takes you right to the app so you can interact with it
Add a new policy
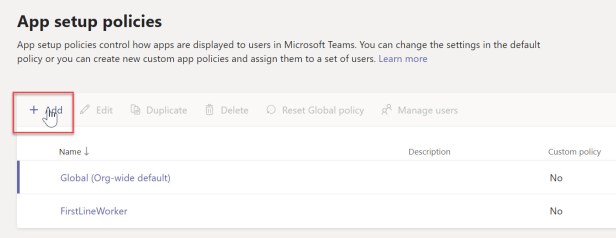
To add a new policy, navigate to app setup policies and click Add
Give the app setup policy a name, such as Operations and search for and add the app you want. Planner in this case


If you want to move an app up and down in the list, select the app and click Move up or Move down. Then save when done

You’ll now see your new policy in the list

Add Members
You can add members one or a few at a time quite easily in the TAC.
Select the policy and click manage users
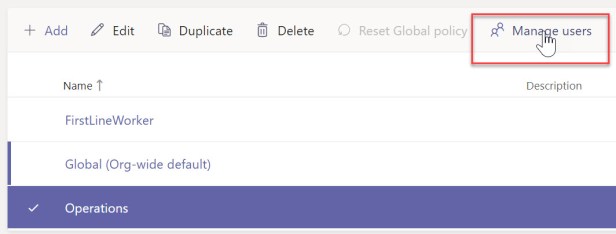
Then search and add a user
You can also add users in bulk using the Azure AD PowerShell and Skype Online PowerShell Modules. Make sure you install and connect to both.
Connect to Azure AD and Skype Online PowerShell
Here’s the normal way. Where you enter your credentials and use them for just this session
$credential = Get-Credential
Connect-AzureAD -Credential $credentials
$sfboSession = New-CsOnlineSession -Credential $credential
Import-PSSession $sfboSession
Or if you connect to them a lot from the same PC, here’s a tip.
First – Save your password as an encrypted file.
You only need to do this once.
Read-Host “Enter Password” -AsSecureString | ConvertFrom-SecureString | Out-File “C:\Users\Admin\Scripts\Password.txt”
Next – Assign the variables for username and password
$Username = “first.last@domain.com”
#$Password = cat “C:\Users\Admin\Scripts\Password.txt” | ConvertTo-SecureString
$Creds = New-Object -TypeName System.Management.Automation.PSCredential -ArgumentList $Username, $Password
Finally – Connect to Azure AD and Skype Online PowerShell
Connect-AzureAD -Credential $Creds
$sfboSession = New-CsOnlineSession -Credential $Creds
Import-PSSession $sfboSession
Now you can grant a policy to multiple users at once
First, get the name of the AD group you want. In this case Contoso Operations
$group = Get-AzureADGroup -SearchString “Contoso Operations“
Then get a list of the members in the AD group
$members = Get-AzureADGroupMember -ObjectId $group.ObjectId -All $true | Where-Object {$_.ObjectType -eq “User”}
Finally, grant the policy to the members of the AD group
$members | ForEach-Object { Grant-CsTeamsAppSetupPolicy -PolicyName “Operations” -Identity $_.EmailAddress}
List the users with a policy
To list all the users with a specific policy, in this case Operations – run the following
Get-CsOnlineUser -Filter {TeamsAppSetupPolicy -eq “Operations“} | select UserPrincipalName
Permission Policies
Permission policies work hand in hand with App setup policies. It lets admins create policies to control what apps are available to Teams users. This is where you can allow or block specific apps by policy. When you block an app, users are unable to install it from the Teams app store.
The global policy has everything turned on and allowed.
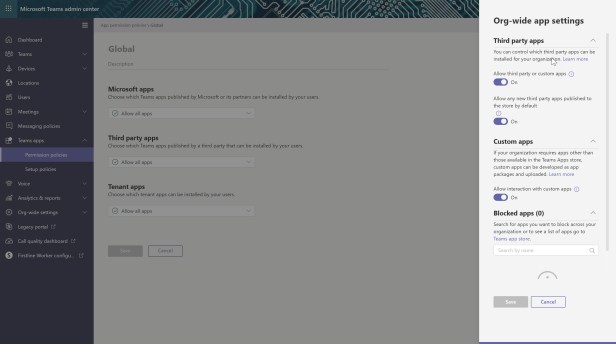
You can create a custom policy to be more restrictive.
Personally, I don’t see a massive problem with allowing all apps. If you restrict users, they will find a way to use the app anyway. With this, at least it is in Teams and that’s a good thing. But I have been asked with this kind of feature in conversations about governance. So some are thinking about it.
Wrap Up
Until now, all a user could see on the rail is a default set of apps that Microsoft added. Now, admins can add line of business apps, by policy, to users that need them. This includes custom apps that aren’t in the store. That’s a subject for another post.
I think this is a great addition to the admin capability in Teams. It might also be nice to have policies where users could choose what apps to display in addition to the default or policy assigned list. But where would it end? If you’re really creative, it would be a good use of a Flow to create a request form to add an app to your rail. I’ll have a think about that.
That’s all folks! Thanks for reading 😊
Resources
Manage app setup policies in Microsoft Teams – Microsoft Docs
Discover more from
Subscribe to get the latest posts sent to your email.



